iOS hacks exposed users unknowingly
Late last week, Google's 'Project Zero' dropped a bomb on the security community: it had discovered a series of complex 0-day attacks happening in the wild against iOS users, which were exploited for years without detection.
In deeply technical posts, the group described a series of "exploit chains" on iOS, in which attackers used a series of bugs, poorly implemented (or partially implemented) features to gain deep access to compromised devices.
All it took for these exploits to compromise a phone? Loading a simple hacked website, which dropped a 'monitoring implant' on the device—an attack vector that was active for two years in various forms, without detection:
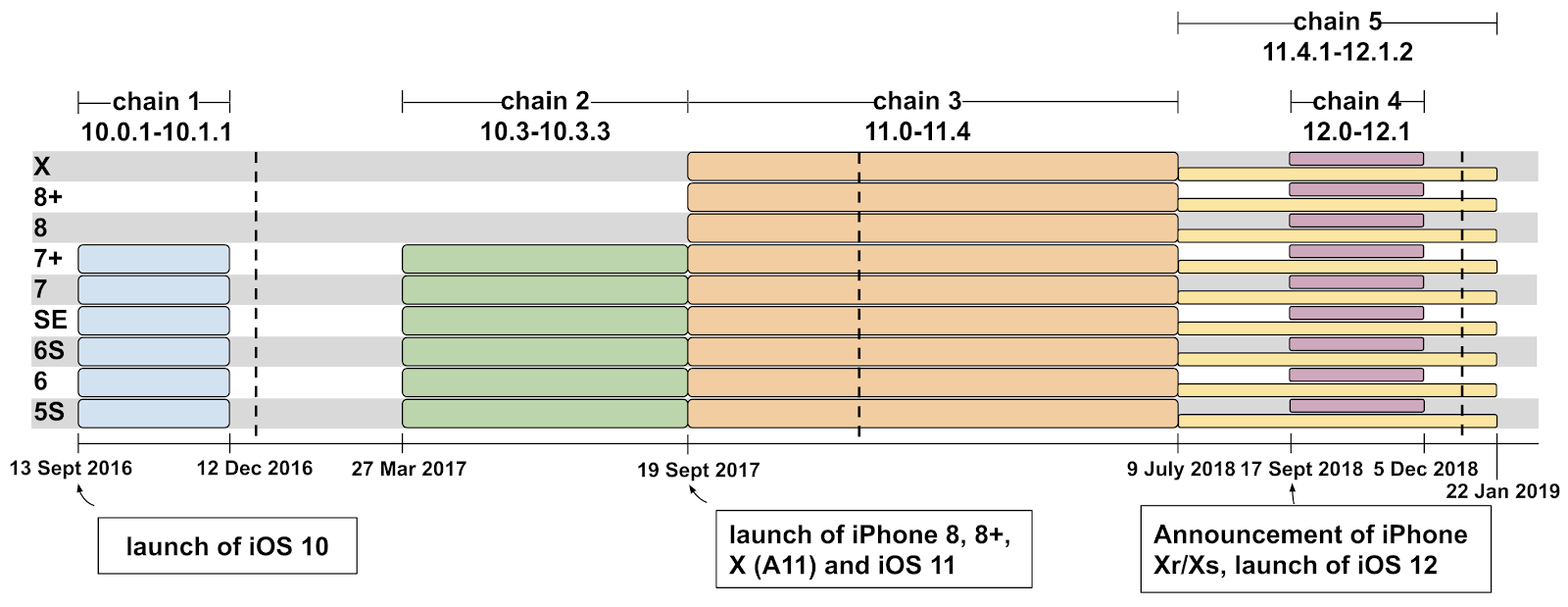
There was no target discrimination; simply visiting the hacked site was enough for the exploit server to attack your device, and if it was successful, install a monitoring implant. We estimate that these sites receive thousands of visitors per week. [...] TAG was able to collect five separate, complete and unique iPhone exploit chains, covering almost every version from iOS 10 through to the latest version of iOS 12.
When the monitoring implant was installed, it was impossible to detect, and incredibly powerful: it was able to steal private data from iMessage conversations to photos and real-time GPS location. That's wild, particularly for an iOS device, and a terrifying new threat.
What was left out of the detailed breakdown of these attacks is what websites were involved in targeting users, a strange detail to leave out when painting a picture of sophisticated attackers. Over the weekend, however, it emerged that the attackers had a very specific target: Uyghur Muslims.
If you're unsure why the Uyghur are a significant target, it's worth reading into what's happening in China right now. Chinese government has created mass detention centers of those in the Uighur community—tightening their grip on a people that might seek to gain independence from China. The Uyghur are subject to intense surveillance, and what some have called 'cultural extermination.'
The skill of the attackers makes sense, with this in mind, as it's likely part of a "state-backed attack" from a government, likely to be China. Forbes later confirmed that the same websites also targeted Android and Windows users—though the Project Zero team said it wasn't able to find any evidence of those systems being attacked.
If you're technically minded, the deep-dive posts into how these attacks unfold are fascinating looks at how complex these exploits actually are, and how far the attackers were willing to go to gain access to a user's device. It's the first time we've ever heard of such a deep attack happening transparently on a mobile device, just by visiting a website.
For its part, Apple fixed the bugs as soon as it was alerted to their existence—but many of the exploit chains point to sloppy code practices, unfinished features that shipped to users, and poor quality assurance processes.
In the last year, Apple has expended a vast amount of resource on tightening up its pipelines, but it's concerning that so many of these bugs existed over the space of such a long time, without detection internally.
So, if you're an iPhone user, what can you do to protect yourself? My advice is simple: ensure you're always up to date with the latest software on your device, and don't put them off. No device will ever be secure against a well-funded, targeted attack—but having the latest and greatest is the best you can do.
Tab Dump
Twitter CEO Jack Dorsey's account was brutally hacked
The moral of this story is that SIM-swapping is a real threat, and two factor security that relies on your phone number is incredibly vulnerable to simple social engineering attacks.
Facebook is testing removing like counts across its platform
Samsung is planning a bunch more foldable phones in the near future
It couldn't even really make the Galaxy Fold work as promised, yet Samsung bluntly forges ahead. Foldable phones are beginning to feel like 3D TV to me: a solution to a problem nobody really asked about.
Must read: Amazon’s Next-Day Delivery System Has Brought Chaos And Carnage To America’s Streets
