Tesla gets cryptojacked
Tesla was 'cryptojacked' in the last few months according to a security firm, along with other giants including an insurance firm and the world's largest SIM card maker.
These companies were all attacked via Kubernetes instances, with default passwords, and a small script to mine crypto was installed on their cloud infrastructure. Apparently, until Tesla was notified, it did not notice the attack because hackers designed it to hide in plain sight, not pushing the CPU too hard and using cloaked endpoints to mine.
I'd never heard of the term cryptojacking until this news emerged, but now that I know the phrase I have a feeling we'll be seeing more of it. As cryptocurrency has seen values soar across different digital coins, people are looking for ways to mine it in cheaper ways than running it themselves. Naturally, at-scale infrastructure of large companies is the perfect place, if you can find a way in.
Building a crypto mining infrastructure of your own is expensive, with massive up-front costs, huge energy bills and ongoing maintenance. This Vice visit to a Chinese Bitcoin mine is a fascinating look at how difficult this is, even if you have the money — so it's easy to see why hackers are interested in, erm, borrowing, other people's servers.
This is still an emerging trend, but here's an example of a water utility's infrastructure being used for mining crypto, too. Where ransomware and viruses were interesting ways to try and make money from end users by exploiting the person directly, this is a new way to extract wealth by taking advantage of their CPU power.
Malware that infects end users to mine coins — WannaMine — is now common, and I imagine far more companies are infected without knowing (antivirus is not equipped for this) than we expect. Infrastructure of larger companies provides a great attack vector simply because they aren't equipped to look for these things across hundreds of thousands of servers, and could prove lucrative if undetected long-term.
The implications of malicious AI
A fantastic paper published by AI startup OpenAI today discusses the implications of artificial intelligence being used for malicious activities. We're not talking about some distant future, but the AI tools available to developers now and in the next five years — here's an example of one plausible social engineering attack:
Victims’ online information is used to automatically generate custom malicious websites/emails/links they would be likely to click on, sent from addresses that impersonate their real contacts, using a writing style that mimics those contacts. As AI develops further, convincing chatbots may elicit human trust by engaging people in longer dialogues, and perhaps eventually masquerade visually as another person in a video chat.
The paper discusses other uses, too, such as "human-like denial of service" in which an AI uses an application in a seemingly legitimate way to overwhelm a server, and fake news reports generated at scale using fabricated video, imagery and audio. Even with our most basic machine learning techniques, many of these attacks are plausible, and difficult to defend against.
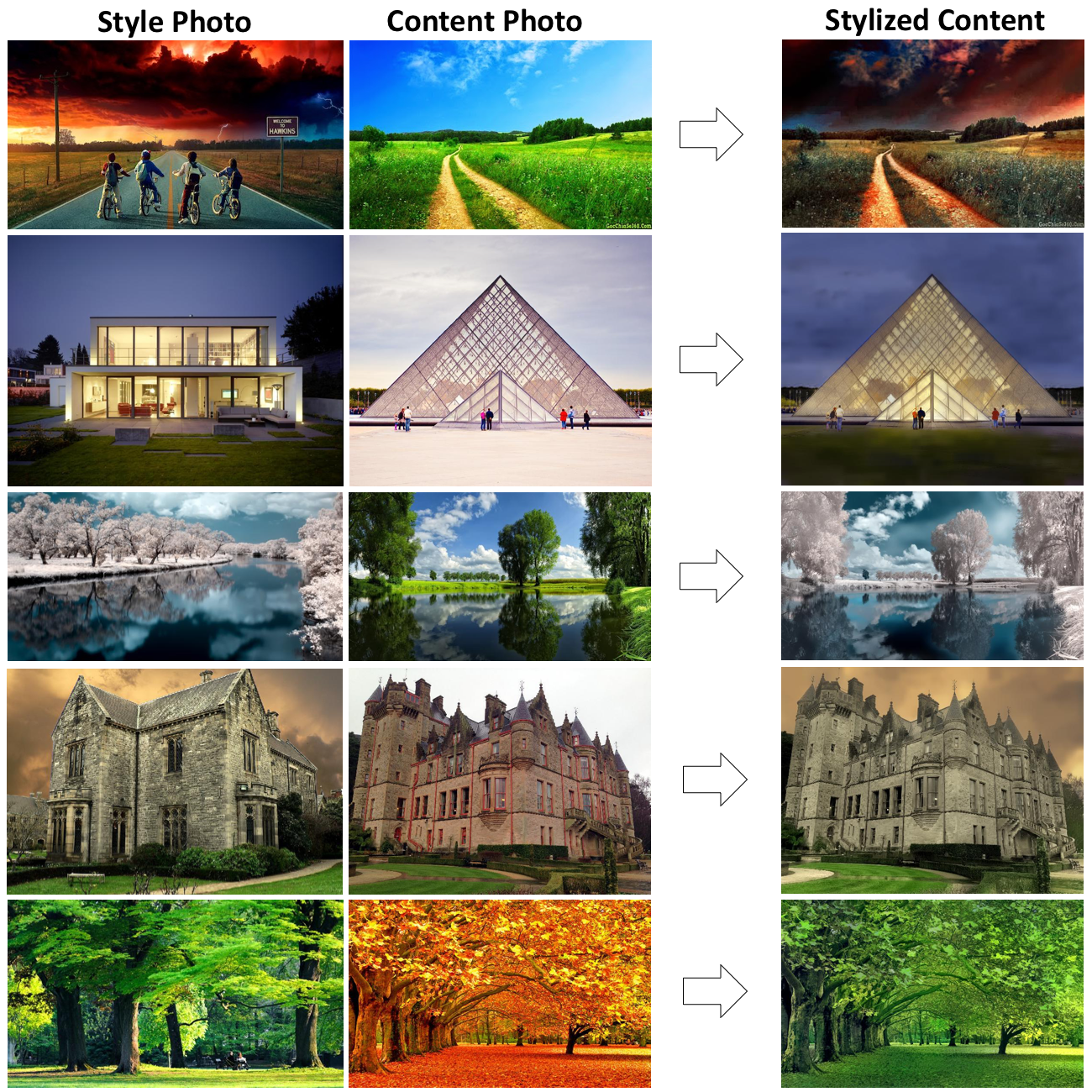
Coincidentally, just this morning NVIDIA published a new AI technique for generating imagery quickly using machine learning. One of the biggest challenges today is that image-based learning can be quite resource intensive or slow, meaning it's difficult to use at scale — but the new technique brings those resource costs down dramatically.
As large technology companies push machine learning harder and show us the new ways it can help our everyday lives, the paper is a sobering read about the other side of these innovations: how bad actors can use these technologies to outwit us entirely at scales that can only be combated by other AI innovations.
The problem presented is that AI innovation is considered a competitive advantage, and small business, along with the individual — you and I — may be left defenseless in the long-term unless the technology to defend against increasingly smart attacks trickles down. It's not difficult to imagine a AI-enabled antivirus platform eventually emerging, for example, if the research is shared.
I highly recommend reading the paper — we're in for a wild ride in the next few years, and I've been blown away by how underprepared we are.
Tab Dump
Microsoft reboots Age of Empires
I lost most of my day yesterday to Age of Empires: Definitive Edition — a fantastic reboot of the original Age of Empires in 4K resolution with high-resolution animations. It's well done, and I'm so full of nostalgia.
Spotify wants to push into hardware
Is this a good idea? Probably not, but if you're the world's biggest music streaming service, it's a logical next step.
Apple plans to buy cobalt directly
There's a rush on the resources required to build batteries right now as Tesla, and other car makers, begin to suck up the supply. Fearing disruption to supply chain, Apple is mulling buying these resources directly from miners.
AT&T plans "5G" implementation in 2018
I'm wary of AT&T's definition of "5G" given what it defines "4G" as (slightly faster 3G, also known as HSPA+) — but it's today saying that 5G will come to a handful of US cities within the year. All we need now is the phones to support it!
